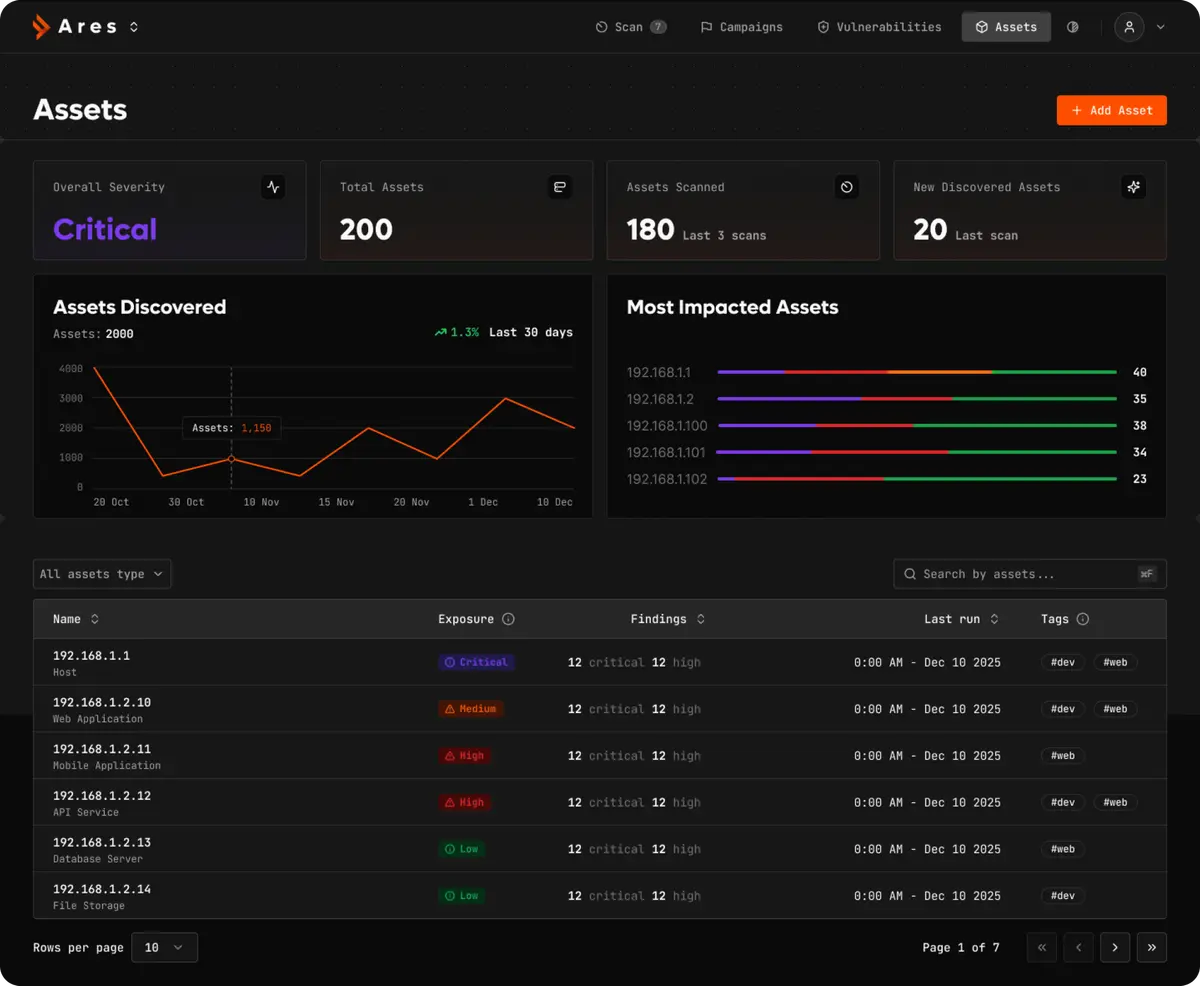
Continuous Attack Surface Management (ASM)
You Can’t Secure What You Can’t See.
Eliminate Shadow IT and blind spots.
ARES autonomously maps your entire digital footprint—from forgotten subdomains to exposed cloud buckets—providing a living, breathing inventory of your external attack surface.
The “Inventory Gap” is Where Breaches Happen.
The Problem
Modern infrastructure is decentralized. Marketing spins up landing pages, developers create testing environments on AWS, and legacy systems sit forgotten in a dusty datacenter.

Spreadsheets are Obsolete
By the time you update your asset inventory, it's already out of date.
Shadow IT is Real
30% of your organization's exposed assets are likely unknown to your security team.
Cloud Sprawl
A single misconfigured Terraform script can expose a private S3 bucket to the world in seconds.
Attackers don't attack the fortress you built. They attack the back door you forgot you had.
Total Visibility.
Continuously Updated.
Recursive Asset Discovery
ARES acts like an external adversary. You provide a single seed domain (e.g., company.com), and our Scout Agent recursively hunts for:
- •Subdomains: (dev.company.com, staging-v2.company.com)
- •Related Root Domains: Acquisitions and subsidiaries you own.
- •Cloud Assets: S3 Buckets, Azure Blobs, and GCP Storage linked to your organization.
- •Dangling DNS: Records pointing to released IP addresses that attackers can hijack.

Deep Fingerprinting
Knowing the IP isn't enough. You need to know what's running on it. ARES identifies:
- •Tech Stack: "Apache 2.4.49", "Jenkins 2.1", "Kubernetes API".
- •CMS Detection: WordPress, Drupal, Joomla versions.
- •WAF Detection: Identifies if an asset is behind Cloudflare, Akamai, or unprotected.

Drift Detection & Alerting
Your attack surface isn't static. ARES takes a baseline snapshot and monitors for changes 24/7.
- •New Port Alert: "Server X just opened Port 3389 (RDP)."
- •New Subdomain: "A new domain promo.company.com just went live."
- •Certificate Monitor: "SSL Certificate for api.company.com expires in 3 days."

From Zero to Full Map in Minutes

Input
Enter your primary organization name or root domain.

Technical Challenge
The Scout Agent queries passive DNS, Certificate Transparency logs, and active WHOIS records

Probe
Satellite Workers ping identified assets to verify they are live and responsive.

Profile
The system fingerprints the software and services running on each asset.

Visualize
Your dashboard populates with an interactive topology graph of your empire.
Strategic Benefits
Instantly assess the technical debt and risk of a company you are acquiring before you sign the deal.
Identify and decommission zombie servers that are costing you money and creating risk.
No agents to install. No credentials needed. This is an "Outside-In" view of your perimeter.
Make Auditors Happy
Stop scrambling before your audit. ARES provides the continuous evidence chains required for



More Use Cases
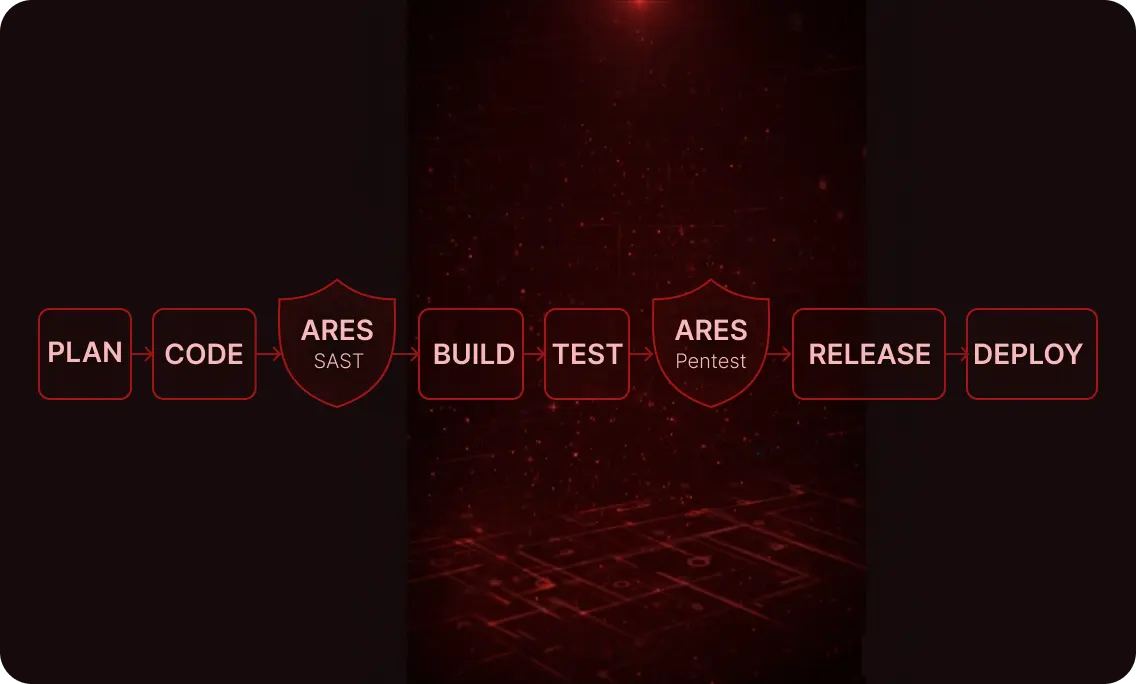
Automated Pentesting (VAPT)
The End of the Annual Pentest.
Replace your slow, expensive, point-in-time consulting engagements with ARES—an autonomous Red Team that tests your defenses 24/7.
Stop Guessing. Start Seeing.
Take control of your perimeter today.