Automated Pentesting (VAPT)
The End of the Annual Pentest.
Security should be a movie, not a photograph.
Replace your slow, expensive, point-in-time consulting engagements with ARES—an autonomous Red Team that tests your defenses 24/7.
The "Pentest Paradox"
The Problem
You are required to pentest your application annually for compliance. But you deploy code daily.

The Risk Window
If you pentest in January and introduce a bug in February, you are vulnerable until next January.
The Cost
Human consulting firms charge $15k - $50k per week. It’s unscalable.
The Result
You are always playing catch-up, getting a PDF report that is obsolete the moment it reaches your inbox.
Attackers don't wait
for your Q4 audit
schedule.Why
should your
defense?
Continuous, Agentic Red Teaming.
Beyond Simple Scanning
Standard scanners check version numbers. ARES acts like a human hacker. It logs in, navigates your application, and tests for:
- •Logic Flaws: IDOR (Insecure Direct Object References), Broken Access Control, and Privilege Escalation.
- •Injection Attacks: SQLi, XSS, and Command Injection (with safe payloads).
- •Auth Bypass: Testing for weak session management and MFA gaps.
Safe, Active Exploitation
Theoretical alerts are useless. ARES validates findings to prove risk without crashing production.
- •The "Sniper" Agent: When a vulnerability is found, the agent attempts a non-destructive exploit (e.g., sleep 5 for SQLi or whoami for RCE).
- •Evidence-Based: If the exploit succeeds, you get a screenshot and a replayable proof-of-concept (PoC). If it fails, the alert is suppressed.

Internal & External Reach
- •Perimeter: Attack from the internet to find what's exposed publicly.
- •Lateral Movement: Deploy a Satellite Worker inside your network to simulate an "Assumed Breach." Watch ARES attempt to pivot from a compromised workstation to your Domain Controller using techniques like Pass-the-Hash.
From Scan to Fix in 4 Steps.
Scope
Define your target (URL, IP Range, or API Endpoint) and set your "Rules of Engagement" (e.g., Safe Mode vs. Full Attack).
Attack
The ARES agents map the surface, identify attack vectors, and execute safe exploits in parallel.
Verify
The "Brain" analyzes the results, discarding false positives and chaining minor bugs into critical attack paths
Report
ARES generates a developer-ready ticket with the exact line of code to fix and a compliance-ready PDF for your auditors.
ARES vs. The Old Way
Make Auditors Happy
Stop scrambling before your audit. ARES provides the continuous evidence chains required for



More Use Cases

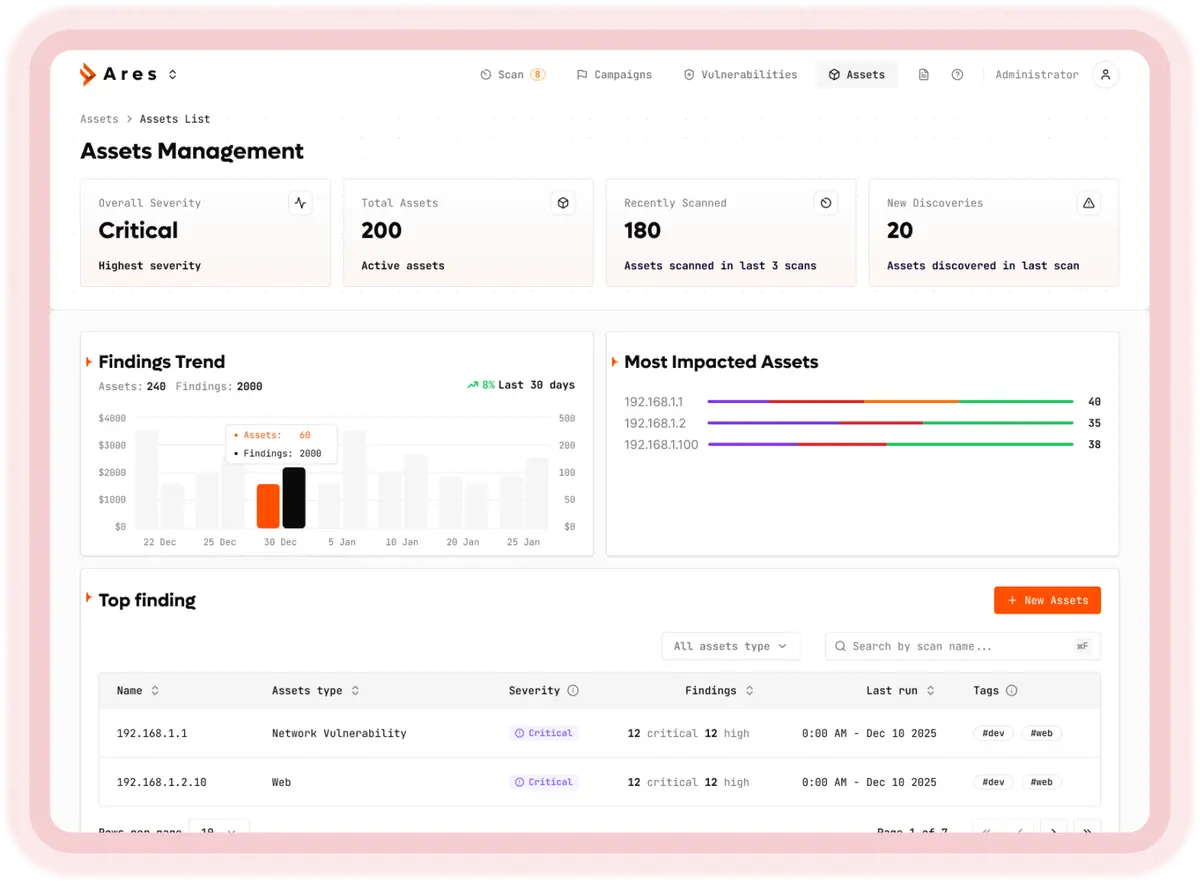
Continuous Attack Surface Management (ASM)
You Can’t Secure What You Can’t See.
ARES autonomously maps your entire digital footprint—from forgotten subdomains to exposed cloud buckets—providing a living, breathing inventory of your external attack surface.
Stop Guessing. Start Seeing.
Take control of your perimeter today.
