Solutions Overview
Together, they create a continuous security loop — from exposure discovery to AI-driven defense and endpoint protection.
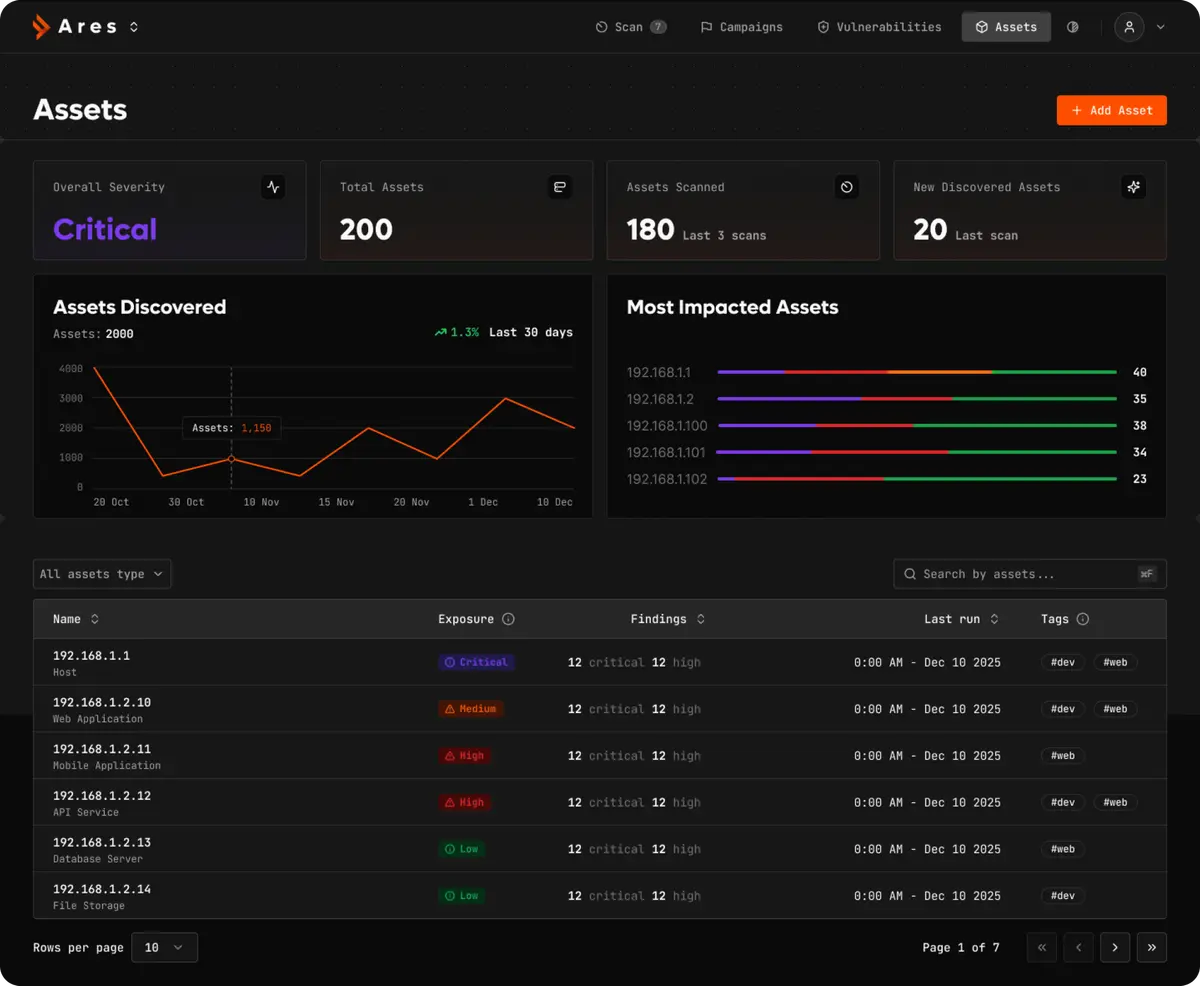
ARES
Continuous Visibility & Offensive Validation
Infrastructure evolves fast. Attackers exploit what remains unseen.
ARES provides a continuous attacker's-eye view and validates security controls at DevOps speed.
Key Capabilities
Continuous Attack Surface Management
Real-time discovery of internet-facing assets
Automated pentesting integrated into CI/CD
High-fidelity security feedback on every build

Outcome
Eliminate blind spots
Secure releases without slowing development
Reduce exploitable exposure

Alethea
AI-Powered Incident Response

SOC teams are overwhelmed by alerts and manual processes.
Alethea organizes your SOC around specialized AI agents — operating under clear human governance.
Key Capabilities
Role-based AI agents (SOC, IR, Threat Hunting)
Detection-as-Code
Real-time telemetry correlation
Context-aware incident enrichment
Human-in-the-loop automation

Outcome
Less alert fatigue
Faster investigations
Semi-autonomous response
Continuous detection improvement

Autosec
Intelligent Endpoint & Digital Protection

Cyber threats target both organizations and individuals — from phishing and malicious sites to identity-based attacks.
AutoSec delivers Swiss-grade digital protection across personal devices and corporate environments.
For Individuals & Families
Safe browsing & phishing protection
Real-time threat blocking
Privacy-first monitoring
Simple, mobile-first experience

For Companies
Employee endpoint protection
Secure browsing for distributed teams
Phishing & malicious domain prevention
Centralized visibility & policy control

Outcome
Reduced human attack surface
Stronger endpoint resilience
Protection beyond the enterprise perimeter

How They Work Together

This creates a continuous security cycle — from infrastructure exposure to AI-driven SOC operations and human-layer defense.



